How BIFA Data Triggers Section 67 Inspection under GST: DGARM’s Risk Analytics Explained
BIFA Analytics: The Catalyst for Intelligence based Action.
Business Intelligence and Fraud Analytics (BIFA) data triggers an inspection under Section 67 by providing the "reasons to believe" required by law to justify a physical verification or search. BIFA acts as the digital intelligence arm (managed by DGARM) that identifies anomalies, which are then disseminated to field officers to initiate enforcement actions.
Here is the step-by-step mechanism of how BIFA data translates into a Section 67 inspection:
1. Identification of High-Risk Parameters (The Trigger)
DGARM (Directorate General of Analytics and Risk Management) uses BIFA to run algorithms on GST returns and external data to flag specific risk parameters. If a taxpayer triggers these "Red Flags," they become a candidate for inspection.
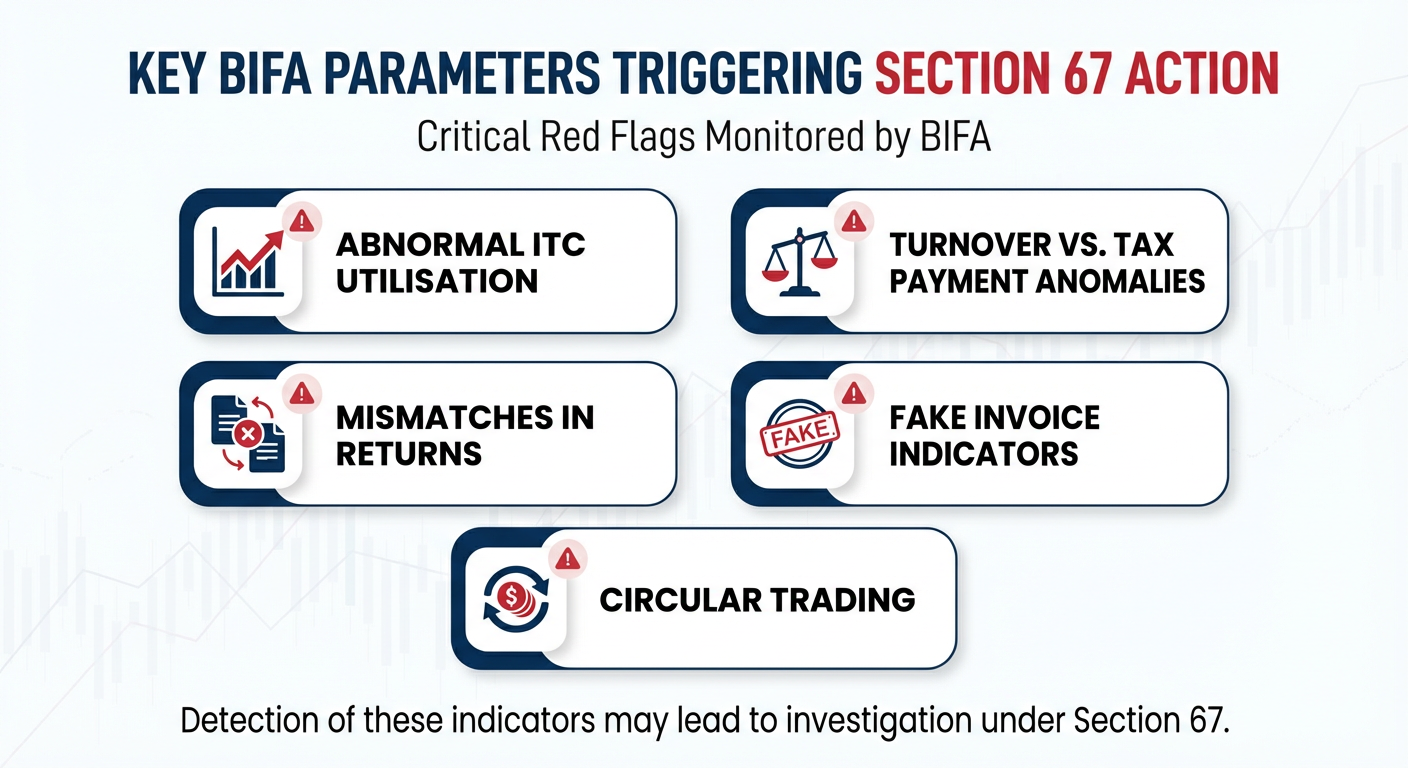
Key BIFA parameters that can trigger a Section 67 action include:
• Abnormal ITC Utilisation: ITC utilisation greater than 95% or 5 times the cash payment.
• Turnover vs. Tax Payment Anomalies: Annual turnover exceeding ₹1 Crore with Nil cash tax payment.
• Mismatches in Returns:
◦ Significant differences between GSTR-1 (Outward) and GSTR-3B (Payment),.
◦ Mismatch between GSTR-3B and E-way Bill data (indicating clandestine removal of goods),.
• Fake Invoice Indicators:
◦ Multiple GSTINs sharing common email IDs, mobile numbers, or addresses.
◦ Ineligible ITC claimed from "Non-Genuine Taxpayers" (NGTPs) whose registration was cancelled ab-initio.
• Circular Trading: Patterns showing ITC moving through a chain of shell companies to inflate turnover without real supply.
2. Operational Workflow (Data to Action)
The transition from data analytics to physical inspection follows a specific administrative flow,:
1. Selection: DGARM selects GSTINs based on the risk parameters mentioned above.
2. Dissemination: This intelligence is sent to the Nodal Officer of the Commissionerate.
3. Distribution: The Nodal Officer distributes the list to the jurisdictional Superintendent (Proper Officer) within 3 working days.
4. Action: The Superintendent analyses the data. While they often start with Scrutiny (Section 61), if the data suggests "suppression of stock," "excess claim of ITC," or "contravention with intent to evade," they can seek approval for Inspection (Section 67).
3. Establishing "Reason to Believe" (Legal Requirement)
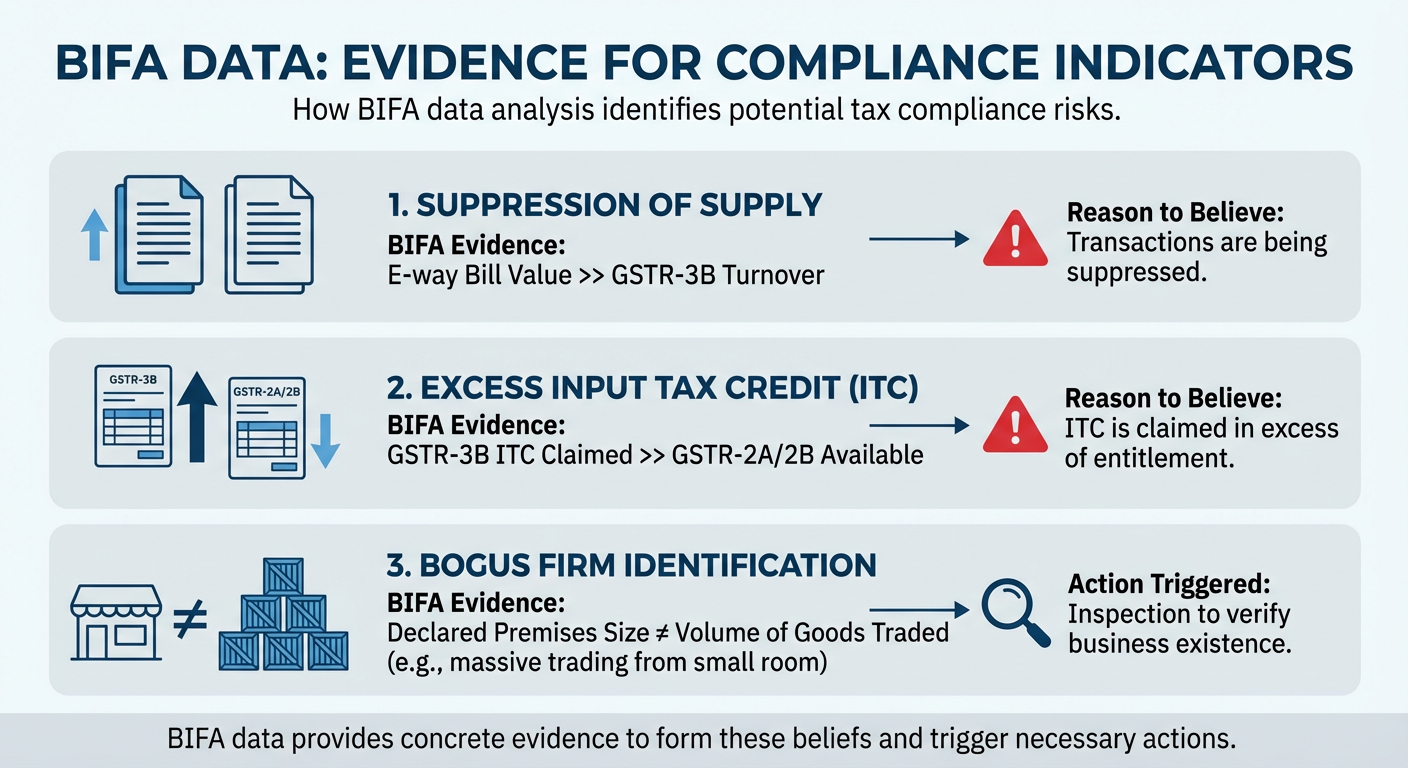
Section 67(1) empowers a proper officer (not below Joint Commissioner) to authorise an inspection only if they have "reasons to believe" that the taxable person has suppressed transactions or claimed excess ITC.
BIFA data provides the concrete evidence to form this belief:
• Suppression of Supply: If BIFA shows E-way bill value is significantly higher than GSTR-3B turnover, it gives reason to believe transactions are being suppressed.
• Excess ITC: If BIFA shows ITC claimed in GSTR-3B is significantly higher than GSTR-2A/2B, it gives reason to believe ITC is claimed in excess of entitlement.
• Bogus Firm: If BIFA identifies a mismatch between the declared premises size and the volume of goods traded (e.g., massive trading from a small room), it triggers an inspection to verify the existence of the business.
4. Escalation from Scrutiny (Section 61) to Inspection (Section 67)
Often, BIFA data first triggers a Scrutiny of Returns under Section 61. The officer issues a notice (ASMT-10) based on the BIFA discrepancies.
• If the taxpayer fails to furnish a satisfactory explanation within 30 days, or fails to take corrective measures, the Proper Officer is explicitly authorised to initiate appropriate action under Section 67 (Inspection, Search, and Seizure),
5. Direct Action in Fraud Cases
In cases of severe fraud detected by BIFA (e.g., a cluster of fake firms created using the same PAN or contact details for passing on ITC), the department may bypass the scrutiny notice and directly launch an investigation and search under Section 67 to prevent the destruction of evidence or the disappearance of the "missing trader",.
Summary:
BIFA converts raw data into actionable intelligence. When this intelligence indicates evasion, suppression, or fraud, it satisfies the statutory requirement of "Reason to Believe", thereby legally authorising the Joint Commissioner to issue FORM GST INS-01 for inspection and search under Section 67
How do authorities use BIFA to detect risky taxpayers
Business Intelligence and Fraud Analytics (BIFA) is the technological arm used by GST authorities (specifically through the Directorate General of Analytics and Risk Management or DGARM) to identify risky taxpayers by running advanced algorithms on the massive volume of data generated by GST returns, E-way bills, and external databases.
Here is how authorities use BIFA to detect tax evasion and risky behaviour:
1. Identifying "Red Flag" Risk Parameters
BIFA utilises specific risk parameters to flag GSTINs for further scrutiny or audit. The sources highlight several key indicators:
-
Abnormal ITC Utilisation: Taxpayers utilising Input Tax Credit (ITC) for more than 95% of their tax liability, or where ITC utilisation is greater than 5 times the cash payment.
-
Turnover vs. Tax Payment Anomalies: Cases where the annual turnover exceeds ₹1 Crore but the tax deposited in cash is Nil.
-
Return Mismatches:
-
GSTR-3B vs GSTR-2A: Significant differences between the credit claimed (3B) and the credit available from suppliers (2A).
-
GSTR-1 vs GSTR-3B: Discrepancies between the liability declared in outward supplies (GSTR-1) and the tax actually paid (GSTR-3B).
-
GSTR-9 vs GSTR-8D: Differences in annual return data.
-
-
E-Way Bill Analytics:
-
Mismatches between the turnover declared in GSTR-3B and the value of goods moved as per E-way bills.
-
Generating a large number of E-way bills but filing no returns (or Nil returns).
-
-
TDS/TCS Mismatches: Turnover declared is less than the turnover implied by Tax Deducted/Collected at Source (TDS/TCS).
2. Detecting Network and Identity Fraud (Fake Invoices)
BIFA is instrumental in unearthing fake invoicing rings and circular trading by analysing network connections:
-
Common Contact Details: It identifies clusters of multiple GST registrations sharing the same email ID, mobile number, or address, which often indicates shell companies controlled by a single entity.
-
Address Verification: Mismatches between the declared premises and the volume of goods transacted (e.g., trading huge volumes from a small room).
-
Circular Trading Patterns: It tracks the movement of ITC through a chain of entities to detect if credit is being passed around without real economic value addition (circular trading).
-
Non-Genuine Taxpayers: It flags ITC claimed from suppliers whose registration has been cancelled ab-initio (from the start) or who are identified as non-filers.

3. Operational Process (DGARM to Field Officer)
The insights generated by BIFA are operationalised through a structured workflow:
-
Selection: DGARM selects GSTINs for scrutiny based on the specific risk parameters mentioned above.
-
Dissemination: This list is sent to the Nodal Officer of the Commissionerate, who distributes it to the proper officer (Superintendent) within 3 working days.
-
Scrutiny: The proper officer scrutinises the returns, relying on this data, and issues a notice (Form GST ASMT-10) to the taxpayer if discrepancies are confirmed.
-
Enforcement: In cases of severe fraud indicators (like fake invoices), the data may lead to direct inspection, search, and seizure under Section 67 rather than just scrutiny.
4. Integration with Other Databases
Authorities use BIFA to cross-link GST data with other statutory databases to find inconsistencies:
-
Income Tax: Comparing turnover declared in GST with Income Tax Returns.
-
Customs (ICEGATE): Verifying IGST on imports shown in GST returns against actual import data from ICEGATE.
-
Bank Records: Analysing banking transactions to see if payments align with the declared supplies.
In summary, BIFA enables authorities to move from manual checking to data-driven enforcement, flagging taxpayers who exhibit statistical anomalies (such as high turnover with low tax payments) or network links to known fraudsters.
- ★★
- ★★
- ★★
- ★★
- ★★

Check out other Similar Posts

CFO Weekly Digest
A weekly newsletter delivering sharp insights, strategic analysis, and critical updates on business, finance, and compliance — designed exclusively for CFOs and Finance Leaders


